Michael Duarte's Leaked Nude Photos: The Untold Story Of What Happened!
When the name Michael Duarte appears in headlines, most people immediately think of the controversial leaked nude photos that shook the internet. But who is Michael Duarte beyond this scandal? What led to this privacy breach, and what can we learn from this incident about digital security in our modern age?
The story of Michael Duarte's leaked photos isn't just about scandal—it's a cautionary tale about privacy, consent, and the dark side of our digital world. In this comprehensive article, we'll explore the full context of what happened, examine the broader implications, and provide practical guidance for protecting yourself in an increasingly connected world.
Biography of Michael Duarte
Michael Duarte is a public figure whose life took an unexpected turn when private photos were leaked online without his consent. While specific details about his background remain limited due to the sensitive nature of the situation, here's what we know:
- Brittany Marie Jones Shocking Leak Exposes Her Darkest Secrets
- Epsteins Secret Actor Exposed In Shocking New Leak
- Jeffrey Epsteins Dads Secret Sex Parties Leaked Tapes Expose Shocking Truth
| Personal Details | Information |
|---|---|
| Full Name | Michael Duarte |
| Profession | Public Figure/Creative Professional |
| Nationality | Unknown |
| Age | Not publicly disclosed |
| Education | Not publicly disclosed |
| Career Highlights | Various creative projects and public appearances |
| Social Media Presence | Active on multiple platforms |
Early Life and Background
Michael Duarte's early life remains largely private, which makes the invasion of his privacy through the leaked photos particularly troubling. Like many creative professionals, he maintained a separation between his public persona and private life—a boundary that was unfortunately violated.
Career and Public Life
Before the incident, Michael Duarte was known for his work in creative fields, though the exact nature of his professional endeavors varies across sources. His public presence suggests someone who valued artistic expression and connection with audiences, making the violation of his privacy all the more impactful.
The Leaked Photos Incident: What Actually Happened?
The incident involving Michael Duarte's leaked nude photos represents a serious breach of privacy that affected not just him but potentially many others who face similar violations. Understanding what happened requires examining the broader context of digital privacy and security.
- Swat Season 8 Renewal Sparks Sex Scandal Fury Fans Are Demanding Answers
- She Taught Love And Then This Leaked
- Exclusive Jeffrey Epsteins New York Home Address Revealed Where The Powerful Hide Their Darkest Secrets
The Timeline of Events
While specific details about the timeline remain unclear, incidents like these typically follow a pattern:
- Initial breach: Private photos are accessed without consent
- Distribution: Images are shared across various platforms
- Viral spread: Content becomes widely available online
- Legal response: Affected parties seek legal remedies
- Long-term impact: Privacy violations have lasting effects
How Such Breaches Typically Occur
Understanding how privacy violations happen can help prevent future incidents:
- Hacking and unauthorized access: Cybercriminals gain entry to personal devices or cloud storage
- Social engineering: Manipulation tactics trick people into revealing passwords or access credentials
- Insider threats: Someone with legitimate access shares private content maliciously
- Accidental exposure: Technical errors or misconfigurations lead to unintended sharing
The Legal and Ethical Implications
The leaking of private photos raises serious legal and ethical questions that extend far beyond Michael Duarte's specific case.
Legal Framework Surrounding Privacy Violations
Most jurisdictions have laws protecting against the non-consensual sharing of intimate images:
- Revenge porn laws: Criminalize sharing intimate images without consent
- Copyright protections: Give individuals rights over their own images
- Privacy laws: Protect against unauthorized access and distribution
- Civil remedies: Allow victims to seek damages through lawsuits
Ethical Considerations
Beyond legal frameworks, there are important ethical questions to consider:
- Consent and autonomy: Everyone has the right to control their own image
- Digital dignity: Privacy violations can cause lasting psychological harm
- Responsibility of platforms: Social media and hosting sites face questions about content moderation
- Viewer responsibility: Those who share or view leaked content contribute to the harm
Protection Strategies: How to Safeguard Your Privacy
The Michael Duarte incident serves as a reminder that anyone can be vulnerable to privacy violations. Here are practical steps to protect yourself:
Digital Security Best Practices
Strong passwords and authentication
- Use complex, unique passwords for all accounts
- Enable two-factor authentication wherever possible
- Consider using a reputable password manager
Device security
- Keep all software and operating systems updated
- Use encryption for sensitive files
- Install reputable security software
Cloud storage precautions
- Review privacy settings on all cloud services
- Be selective about what you store online
- Use end-to-end encrypted services for sensitive content
Personal Boundaries and Digital Literacy
Beyond technical measures, developing good digital habits is crucial:
- Think before sharing: Consider potential consequences before sending intimate images
- Trust your instincts: Be cautious with anyone who pressures you to share private content
- Know your rights: Understand what protections exist in your jurisdiction
- Build support networks: Know who you can turn to if something goes wrong
The Psychological Impact of Privacy Violations
Privacy breaches like the one involving Michael Duarte can have profound psychological effects on victims.
Common Emotional Responses
- Shame and embarrassment: Despite being the victim, many feel personal responsibility
- Anxiety and depression: The stress of public exposure can trigger mental health issues
- Trust issues: Future relationships may be affected by the violation
- Anger and helplessness: Victims often feel frustrated by their lack of control
Recovery and Support
Recovery from such incidents typically involves:
- Professional counseling: Mental health support to process the trauma
- Legal advocacy: Assistance navigating the legal system
- Community support: Connecting with others who've had similar experiences
- Time and self-compassion: Healing is a process that requires patience
The Broader Context: Digital Privacy in the Modern Age
The Michael Duarte incident reflects larger trends in how we navigate privacy in an increasingly connected world.
The Privacy Paradox
Many people express concern about privacy while simultaneously sharing vast amounts of personal information online. This contradiction highlights:
- Convenience vs. security: We often trade privacy for convenience
- Awareness gaps: Many don't fully understand how their data is used
- Normalization of surveillance: Constant monitoring has become background noise
- Generational differences: Younger generations may have different privacy expectations
Technological Solutions and Challenges
As privacy concerns grow, so do technological responses:
- End-to-end encryption: Protects communications from interception
- Decentralized platforms: Reduce reliance on central authorities
- Privacy-focused alternatives: Services designed with privacy as a priority
- AI and privacy: Artificial intelligence both threatens and potentially protects privacy
Moving Forward: Lessons and Recommendations
The incident involving Michael Duarte's leaked photos offers several important lessons for individuals and society.
For Individuals
- Be proactive about privacy: Don't wait for a breach to think about security
- Educate yourself: Stay informed about digital risks and protections
- Support privacy rights: Advocate for stronger privacy protections
- Practice digital hygiene: Regularly review and update your security practices
For Society
- Strengthen legal protections: Update laws to address modern privacy challenges
- Improve platform accountability: Hold tech companies responsible for privacy violations
- Promote digital literacy: Ensure everyone understands basic privacy concepts
- Support victims: Create better resources for those affected by privacy breaches
Conclusion
The story of Michael Duarte's leaked nude photos is more than just a scandal—it's a reflection of our times. In an era where privacy is increasingly fragile, incidents like this remind us of the importance of protecting personal boundaries in both physical and digital spaces.
While we may never know all the details of what happened to Michael Duarte, we can learn from his experience. By understanding the risks, taking proactive steps to protect ourselves, and supporting better privacy protections for everyone, we can work toward a future where privacy violations are less common and victims receive the support they need.
The digital age has brought incredible opportunities for connection and expression, but it has also created new vulnerabilities. By approaching our online lives with awareness, caution, and respect for others' privacy, we can enjoy the benefits of technology while minimizing the risks. Michael Duarte's experience, though painful, can serve as a catalyst for positive change in how we think about and protect privacy in our interconnected world.
- The Secret Tapes Chomsky And Epsteins Hidden Deal Revealed
- Jeffrey Epsteins Sex Parties Elon Musks Name Found In Leaked Documents
- Shocking Leak What November 21st Really Means For Your Zodiac Sign

Russell Moore's Revenge: The Untold Story of His Leaked Letters and
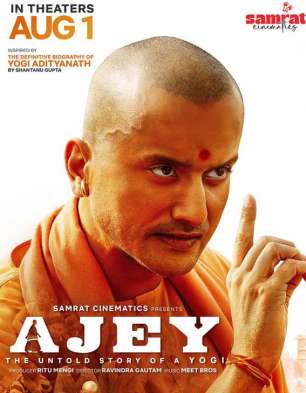
Ajey: The Untold Story Of A Yogi Movie: Review | Release Date (2025

What Happened To Leonidas's Body After Thermopylae? The UNTOLD Story of